How Budgie Keeps Your Financial Data Off the Cloud
A technical deep-dive into Budgie’s offline-first architecture, explaining how SQLite, AES-256 encryption, and device-to-device sync keep your financial data completely private.
A technical deep-dive into Budgie’s offline-first architecture, explaining how SQLite, AES-256 encryption, and device-to-device sync keep your financial data completely private.
When you open most expense tracking apps, something happens in the background that you might not notice: your transaction data, account balances, and spending habits are uploaded to servers you do not control. These servers might be located anywhere in the world, managed by teams you have never met, and protected by security practices you cannot verify.
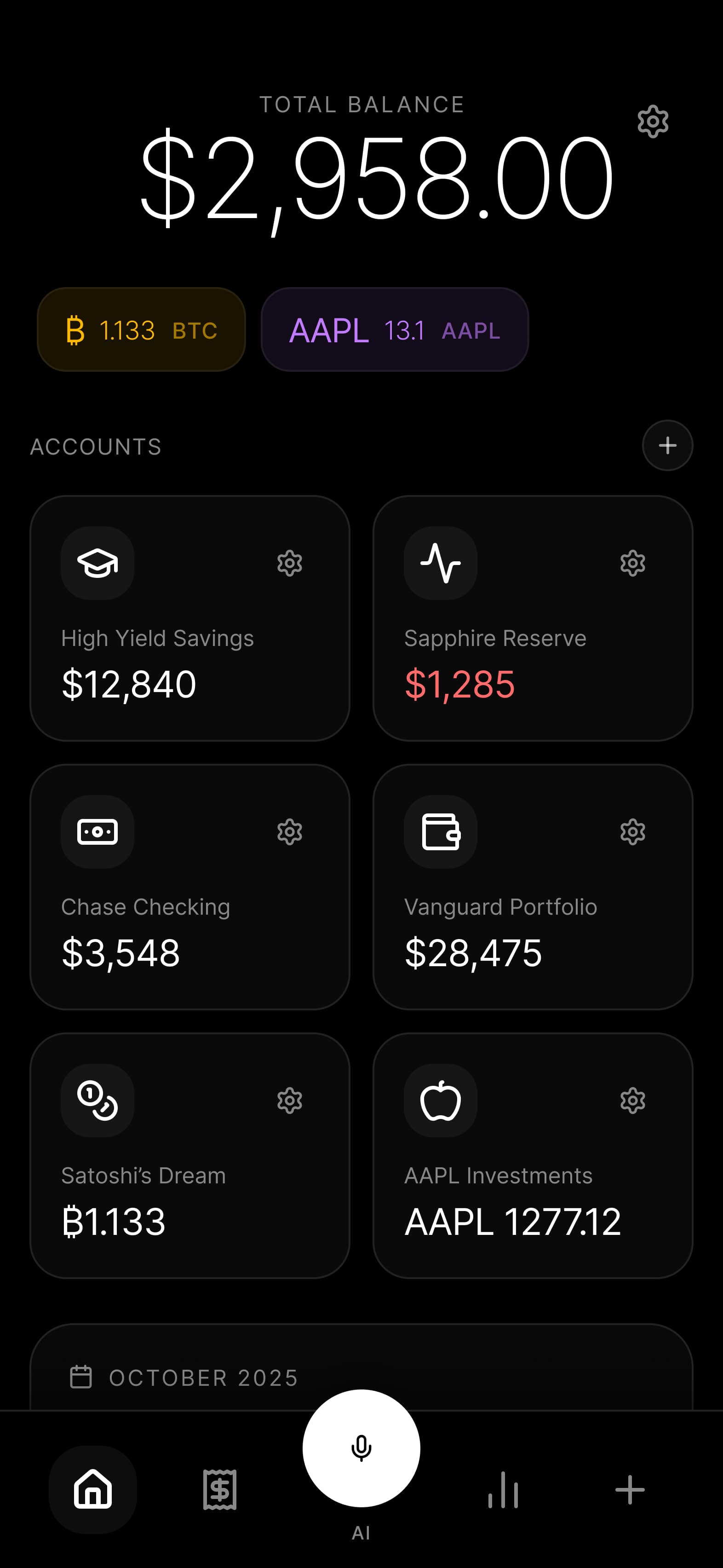
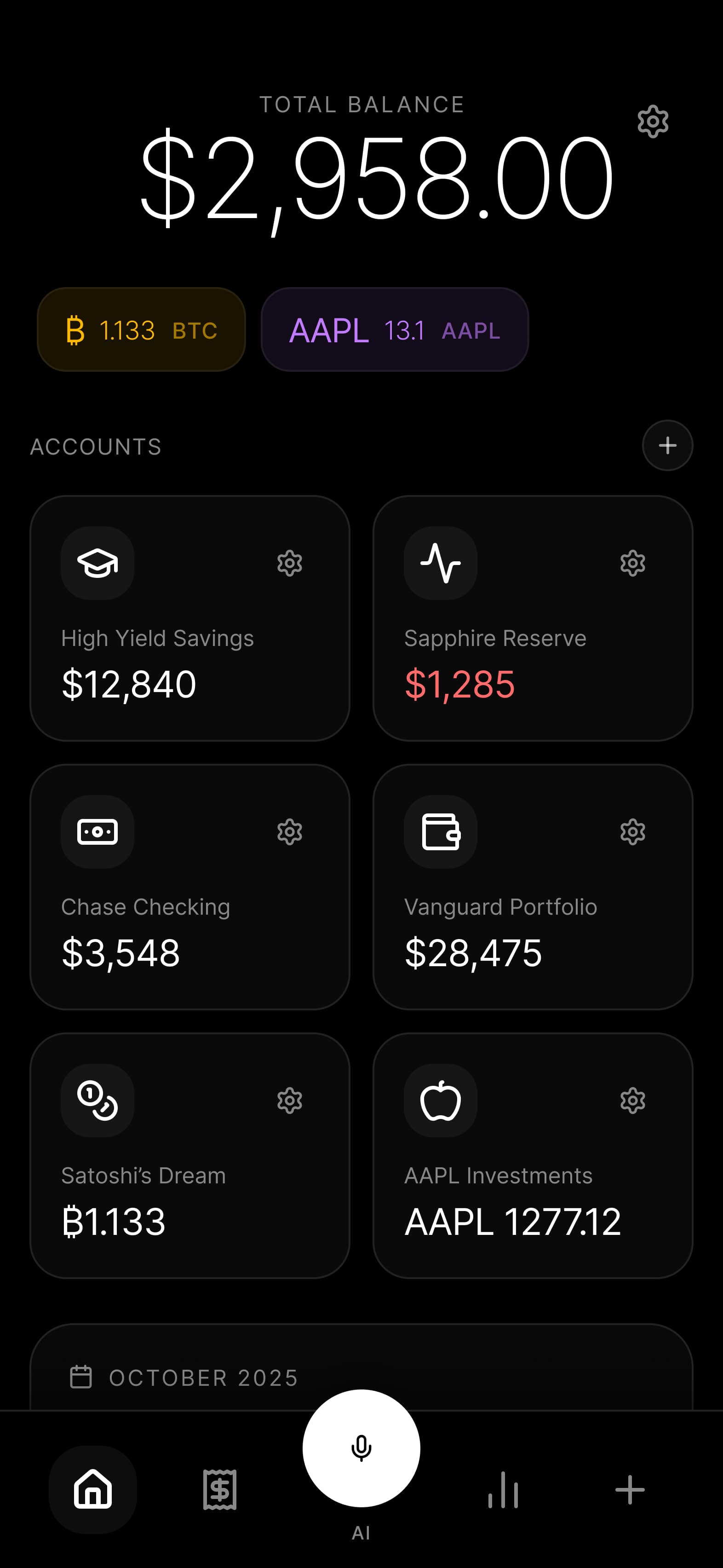
Budgie takes a fundamentally different approach. Your financial data never leaves your device. This is not a marketing statement or a simplified explanation of a more complex reality. It is a literal description of how the app works at the code level.
In this article, we will walk through exactly how Budgie keeps your financial data off the cloud. We will cover the database architecture, encryption implementation, sync mechanisms, and security practices that make this possible. If you are evaluating Budgie and want to understand what you are trusting, this guide will give you the complete technical picture.
At the heart of Budgie is a local-first architecture built on SQLite, the most widely deployed database engine in the world. SQLite runs on billions of devices and has been battle-tested for over two decades. It is the same database that powers your browser history, your mobile contacts, and countless other applications that require reliable local storage.
Cloud-based expense trackers typically use databases like PostgreSQL, MySQL, or MongoDB running on remote servers. When you add a transaction, it travels over the internet to a data center, gets processed, and then a confirmation returns to your device. This architecture creates several problems:
Network dependency: You cannot access your data without an internet connection. Try adding an expense while underground on the subway or in an area with poor coverage, and you are stuck.
Latency: Every operation requires a round trip to the server. Even with fast connections, this adds noticeable delay to every action you take.
Data exposure: Your financial data exists on servers that could be breached, subpoenaed, or accessed by employees with administrative privileges.
Service dependency: If the company shuts down, gets acquired, or experiences extended outages, your access to your own financial history disappears.
SQLite eliminates all of these problems. The database file lives on your device, operations happen in microseconds, and your data remains under your physical control.
When you create a transaction in Budgie, here is what happens at the technical level:
There is no background sync silently uploading your data. There is no analytics event recording what you spent money on. The operation begins and ends on your device.
The SQLite database file is stored in a protected directory that only Budgie can access. On iOS, this is the app’s sandboxed Documents directory. On Android, it is the internal app storage that other applications cannot read.
Many apps that claim to respect privacy still collect anonymized usage data, crash reports, or analytics events. These data streams can reveal more than you might expect. Even without your name attached, patterns in your usage can be identifying.
Budgie includes zero analytics SDKs. We do not use Firebase Analytics, Mixpanel, Amplitude, or any similar service. We do not collect crash reports through third-party services. We do not record which features you use, how often you open the app, or what categories you spend money in.
This is not because we do not care about improving the product. We do. But we have chosen to gather feedback through direct user conversations and open-source community input rather than surveillance infrastructure.
Storing data locally is the first layer of protection. Encryption is the second. Even if someone gains physical access to your device, your financial data should remain unreadable without your authorization.
Budgie encrypts your database using AES-256, the same encryption standard used by governments and financial institutions worldwide. AES-256 has never been broken by any publicly known attack. A brute-force attempt to crack a 256-bit key would require more energy than exists in the observable universe.
When your database is encrypted, the file on disk appears as random binary data. Without the correct key, it is computationally infeasible to extract any meaningful information.
The encryption key never leaves your device and never touches our servers because we do not have servers that handle user data. Here is how key management works:
Key derivation: Your encryption key is derived from your device credentials using industry-standard key derivation functions. This means the key is unique to your device and cannot be reconstructed elsewhere.
Secure storage: The derived key is stored in platform-specific secure enclaves. On iOS, this is the Keychain. On Android, it is the Android Keystore backed by hardware security modules when available.
Key isolation: Each device has its own encryption key. There is no master key that could decrypt all user databases, because such a key does not exist.
Memory protection: Keys are held in memory only when needed for database operations and are cleared when the app is backgrounded or closed.
This architecture means that even if someone steals your device, they cannot read your financial data without also compromising your device’s security (unlocking it with your biometrics or passcode).
Database encryption protects your data in several scenarios:
Device theft: A thief cannot plug your phone into a computer and extract readable financial data.
Forensic analysis: Even with sophisticated forensic tools, the encrypted database cannot be meaningfully analyzed without the key.
Backup exposure: If your device backup is compromised, the encrypted database within it remains protected.
App data extraction: On rooted or jailbroken devices where app sandboxing can be bypassed, encryption still protects the data.
One of the most common questions about offline-first apps is: how do I get my data onto a new device? Budgie handles this through device-to-device sync with no cloud intermediary.
When you want to transfer your data to a new device, Budgie uses direct peer-to-peer communication. Here is the process:
The critical point is that at no point does readable financial data travel through any third-party infrastructure. Even the temporary relay used for discovery when devices are not on the same network sees only encrypted data that it cannot interpret.
Traditional cloud sync relies on a central server to be the source of truth when conflicts arise. If you edit a transaction on two devices, the server decides which version wins.
Budgie uses a different approach based on Conflict-free Replicated Data Types (CRDTs) and operational transforms. Each change is recorded as an operation with a timestamp and device identifier. When syncing:
This means you can use Budgie on multiple devices that occasionally sync when they are on the same network, and your data will eventually converge to a consistent state without data loss.
We will be direct about the tradeoffs. Cloud sync is more convenient. You do not need to be on the same network. You do not need to initiate a sync manually. Changes propagate automatically in the background.
Budgie’s device-to-device sync requires more user involvement. You need to explicitly trigger sync when you want data to transfer. Both devices need to be accessible, either on the same local network or both connected to the internet for the relay-assisted handshake.
We believe this tradeoff is worth it for financial data. The convenience of automatic cloud sync comes at the cost of your data existing on servers you do not control. For many types of data, that tradeoff is acceptable. For your complete financial history, we think local control is worth the extra steps.
Most expense tracking apps that offer bank synchronization use Plaid, Yodlee, or similar aggregation services. These services work by collecting your bank credentials or OAuth tokens and then accessing your account on your behalf. Your transaction history flows through their servers before reaching your app.
Budgie takes a different approach to bank data import.
The most private way to get bank data into Budgie is manual import. Most banks allow you to download transaction history in standard formats like CSV, OFX, or QIF. You download this file directly from your bank, and Budgie imports it locally on your device.
No third party ever sees your bank data. No credentials are shared with anyone. The process is:
The parsing and categorization happen entirely on your device. Budgie includes pattern recognition for common transaction formats from major banks, and you can customize categorization rules that apply locally.
We could have integrated Plaid. It would have been easier for us to implement and more convenient for users. One button click and your transactions appear automatically.
But that convenience comes with costs that are often invisible to users:
Data retention: Aggregation services retain your transaction history on their servers, sometimes indefinitely.
Third-party access: Your bank data flows through infrastructure operated by companies whose business model depends on data.
Credential exposure: Some services store your bank credentials, creating a high-value target for attackers.
Regulatory risk: Your data becomes subject to the legal jurisdictions and requests wherever those servers are located.
Manual import takes more effort, but it ensures that your bank data follows the same privacy guarantees as the rest of Budgie: it never leaves your device, and no third party ever has access.
We are exploring options for assisted bank import that would maintain privacy guarantees. This might include local parsing of bank emails, integration with open banking APIs that use OAuth without credential sharing, or partnerships with privacy-focused financial data providers that operate under strict data handling agreements.
Any future solution will maintain our core principle: your financial data remains on your device, encrypted, and under your control.
Everything we have described in this article can be verified by examining our source code. Budgie is open source, and we believe this transparency is essential for any application that handles sensitive financial data.
Our complete source code is available on GitHub. You can find it by visiting our open-source section where the repository link is provided.
The repository includes:
There are no private repositories containing the “real” code that handles your data differently. What you see is what runs on your device.
If you want to verify our privacy claims, here are the key areas to examine:
Network layer: Search for any HTTP clients, fetch calls, or socket connections. You will find that network usage is limited to exchange rate fetching (which does not include any user data), optional device-to-device sync (encrypted end-to-end), and app update checks (no user data transmitted).
Database layer: Examine the Drizzle ORM schemas and repository classes. You can trace exactly how data flows from user input to database storage, all locally.
Analytics and tracking: Search for any analytics SDK initialization. You will not find Firebase, Amplitude, Mixpanel, or any similar integration.
Third-party SDKs: Review the dependency tree. We minimize external dependencies, and each one is selected carefully to avoid privacy-invasive libraries.
We welcome security researchers, privacy advocates, and technically curious users to examine our code. If you find something that contradicts our privacy claims, we want to know about it.
We are working toward fully reproducible builds, which would allow you to compile the source code yourself and verify that the binary matches what is distributed through app stores. This is the gold standard for verifiable software, and it is on our roadmap.
Beyond the architecture itself, how we develop and maintain Budgie matters for your security.
Every dependency in Budgie is evaluated for privacy implications before inclusion. We specifically avoid:
This significantly limits our choices compared to developers who do not prioritize privacy. But it means you can trust that opening Budgie is not silently reporting your activity to a dozen different data collection services.
Open source software depends on a chain of dependencies, and any link in that chain could introduce vulnerabilities or privacy issues. Our security practices include:
Regular dependency audits: We use automated tools to scan for known vulnerabilities in our dependency tree.
Minimal dependency philosophy: We prefer implementing functionality ourselves over adding dependencies, reducing attack surface.
Source review for critical paths: Dependencies that touch encryption, database operations, or any sensitive data paths are manually reviewed.
Lock file integrity: Dependency versions are locked to prevent supply chain attacks through compromised package updates.
If you discover a security vulnerability in Budgie, we want to work with you to fix it responsibly. Contact information for security reports is available in our repository. We commit to:
Your data exists only on your device. If you lose your phone without having synced to another device or created an encrypted backup, your data is lost. This is the privacy tradeoff: we cannot help you recover data because we do not have it. We recommend regular backups to your own storage.
We cannot provide your data to law enforcement or anyone else because we do not have it. There is no server to subpoena, no database to query, and no backup to hand over. Your data is on your device, protected by your device security and Budgie’s encryption.
Our encryption uses standard library implementations of AES-256 from platform security frameworks (iOS CryptoKit, Android Keystore). These implementations are developed and audited by Apple and Google. Our integration is documented in the open source code for community review.
Budgie supports exporting your complete financial history in standard formats (CSV, JSON). You own your data, and you can take it with you. The export happens locally, producing a file you can use with any other application.
We collect anonymized crash reports through app store mechanisms (App Store Connect for iOS, Google Play Console for Android). These reports do not contain financial data. We use them to fix bugs that cause crashes. No other data is collected through any channel.
End-to-end encrypted cloud sync would require servers to store encrypted blobs. While the content would be encrypted, metadata would still be visible: when you sync, how much data you have, sync patterns that might reveal usage habits. Device-to-device sync eliminates even this metadata exposure.
Your financial data tells a complete story about your life. Where you live, where you shop, what you care about, what struggles you face, what hopes you have. This data is valuable precisely because it is so revealing.
Budgie exists because we believe you should not have to trade this intimate information for the convenience of expense tracking. Every architectural decision, from SQLite to local encryption to device-to-device sync, is designed to keep this information where it belongs: under your control.
We have described our approach in detail not because we think everyone needs to understand database architectures, but because we believe you deserve to know exactly what an app does with your sensitive data. We invite you to verify our claims, examine our code, and hold us accountable to the privacy standards we have set.
For more details on our security architecture, visit our security section. To see the complete source code and verify everything we have described, check out our open-source section.
Ready to try an expense tracker that respects your privacy? Join the waitlist and be among the first to experience financial management without surveillance.
2025-01-27
A detailed technical analysis of how cloud-based budgeting apps collect, share, and expose your financial data through Plaid integrations, data breaches, and third-party aggregation.
Read article→2025-02-12
Learn why open-source matters for financial software, how to audit apps yourself, and how Budgie's transparent development protects your financial data.
Read article→Join the Budgie waitlist and be the first to experience truly private expense tracking.
Join Waitlist